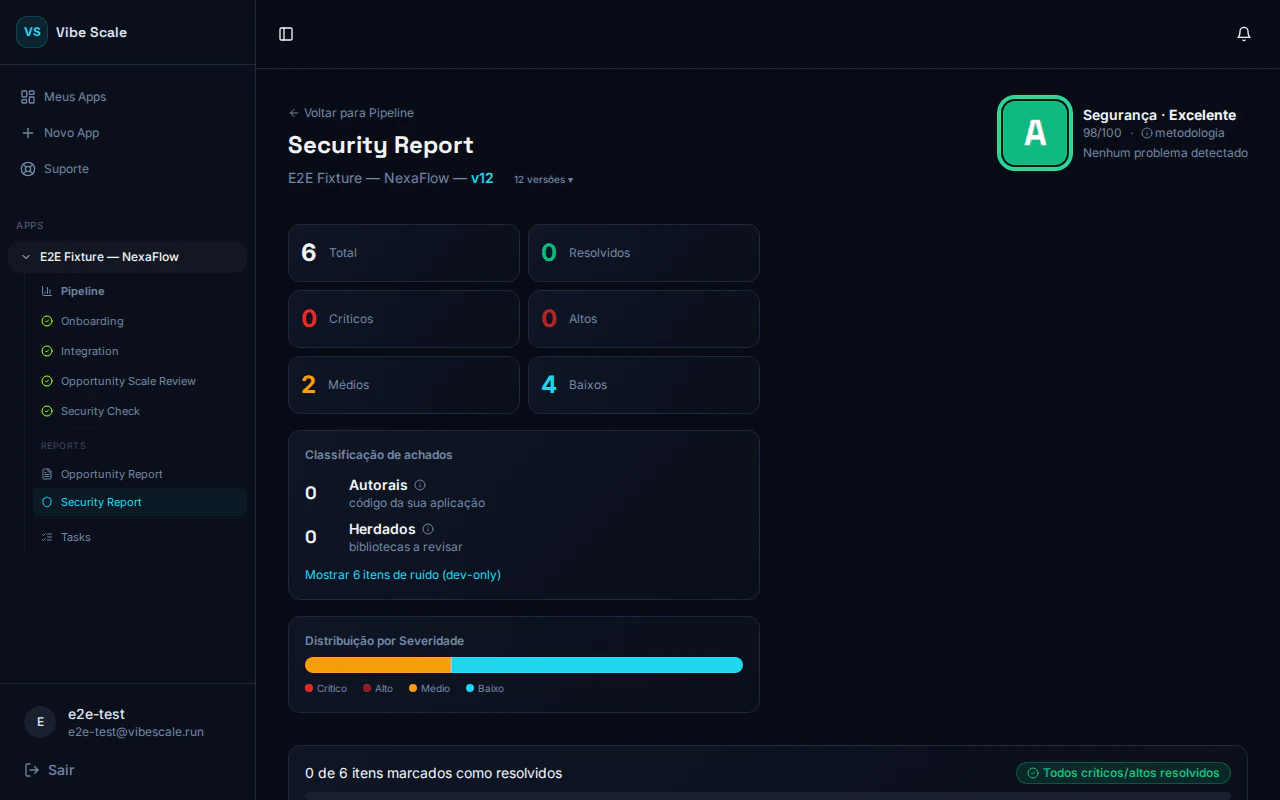
Grade and score
The report header displays:- Grade letter — from A (best) to E (critical):
| Grade | Label |
|---|---|
| A | Excellent |
| B | Good |
| C | Acceptable |
| D | Attention |
| E | Critical |
- Numeric score — from 0 to 100.
- Summary — a sentence reflecting the overall state:
- “X authored items need attention”
- “Inherited dependencies only — no urgent actions”
- “No issues detected”
Finding categories
Each finding belongs to one of the three categories below. Understanding the difference is the most important step to prioritizing correctly.Authored — problems in your code
Authored — problems in your code
Inherited — library vulnerabilities
Inherited — library vulnerabilities
Flaws in third-party packages your project imports. Worth reviewing — especially critical and high ones — but fixing them requires updating the package version, not changing your own code directly.
Noise — development tools
Noise — development tools
Findings from packages used only in development that never reach production. Do not affect your score. Hidden by default.To view them, click “Show X noise items (dev-only)” at the bottom of the list.
Severity levels
Within each category, findings are ordered by severity:| Severity | Meaning |
|---|---|
| Critical | Immediate risk of compromise. Fix before anything else. |
| High | Serious risk that should be resolved in the next sprint. |
| Medium | Moderate risk. Plan the fix. |
| Low | Limited impact. Fix when convenient. |
| Minimal | Informational. Very low practical impact. |
EPSS badges
Some findings display an additional real exploitation risk badge:🔴 Active exploitation
≥ 90th percentile EPSS. This finding is among the most likely to be exploited in the next 30 days, according to FIRST.org data. Prioritize the fix immediately.
🟠 Elevated risk
Between the 50th and 90th percentile. Above the industry median. Worth scheduling the fix.
EPSS measures the real probability of exploitation, not just technical severity. A Medium severity finding with an Active exploitation badge may be more urgent than a High finding without one.
Finding details
Click any finding to see:- Title and severity badge (e.g., CRITICAL RISK, HIGH RISK)
- Problem description
- Affected location — file path or module name
- Code snippet — when available
- Fix suggestion
- Classification — Authored / Inherited / Noise
Available actions
Mark as resolved
Click the checkbox next to a finding to mark it as resolved after applying the fix.Create a Kanban task
Click Create Task to send the finding directly to your Kanban board. Priority is mapped automatically:| Severity | Kanban priority |
|---|---|
| Critical | P1 |
| High | P2 |
| Medium | P3 |
